Digitising the nuclear supply chain
Using TODA/ADOT to digitise supply chains to be efficient, P2P, interoperable and not sacrifice security, privacy or safety
(6 min read)
Before the internet, games were slightly more primitive and one of the children’s games that demonstrated the friction of pushing integrity and trust through multiple parties was ‘Broken Telephone’. You didn’t have to line up many people and whisper a message starting from one end to the other for the message to degrade or be lost entirely.
This problem plays out in our modern markets for high risk and high value assets and examples are everywhere. Take the nuclear power supply chain as an example. Understandably we would all want stringent quality and safety standards in place for all the critical parts composing our nuclear power plants. Like with planes, trains, medical equipment, pharmaceutical drugs, or protective wear and equipment for first responders, small errors can result in loss of life. If we were to take something simple and essential like a pressure gauge, it’s something you absolutely need to work properly and if we thought about what risks could result from a faulty pressure gauge in a nuclear plant here is just a few:
Unauthorised or uncertified suppliers could create risks.
Faulty or forged equipment could be introduced even if the documentation is correct.
The documentation could also be forged or incorrect.
Often certified and inspected equipment have appended stickers, stamps and other marks which are also at risk of manipulation or forgery.
What results from the safety requirement and risks are: a lot of complexity which creates its own safety risks; necessarily detailed and inflexible regulations and standards; multiple tiers of suppliers and regulators; and a resulting process that is slow, full of friction, and expensive. That expense gets tacked onto the $/KWh consumers pay for directly in their power bill.
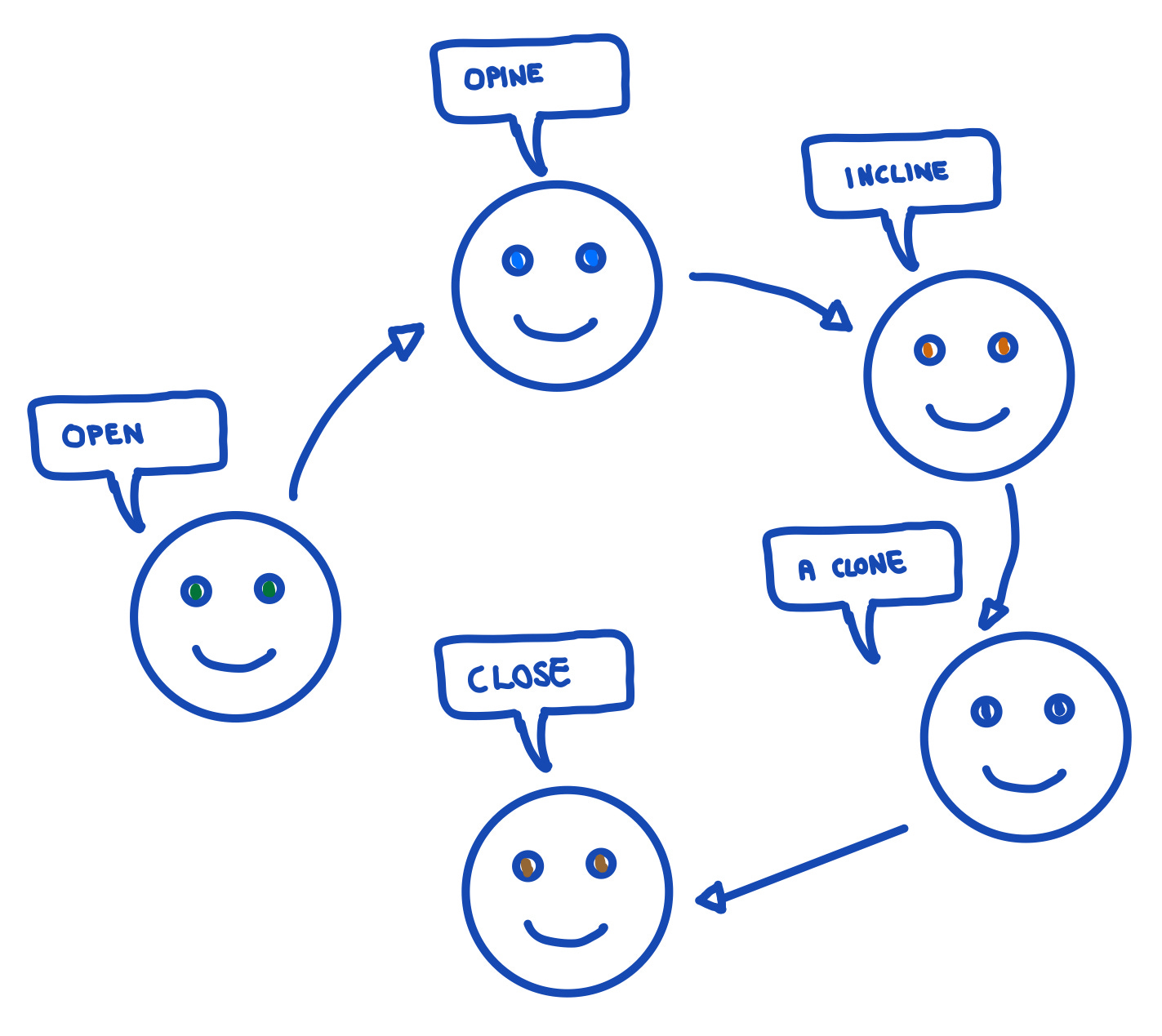
Imagine at a power plant we then wanted to be able to securely and efficiently verify that a pressure gauge was built by authorised supplier(s), with the right materials, transported, installed and maintained correctly by certified personnel; and with all the required safety and performance inspections and audits:
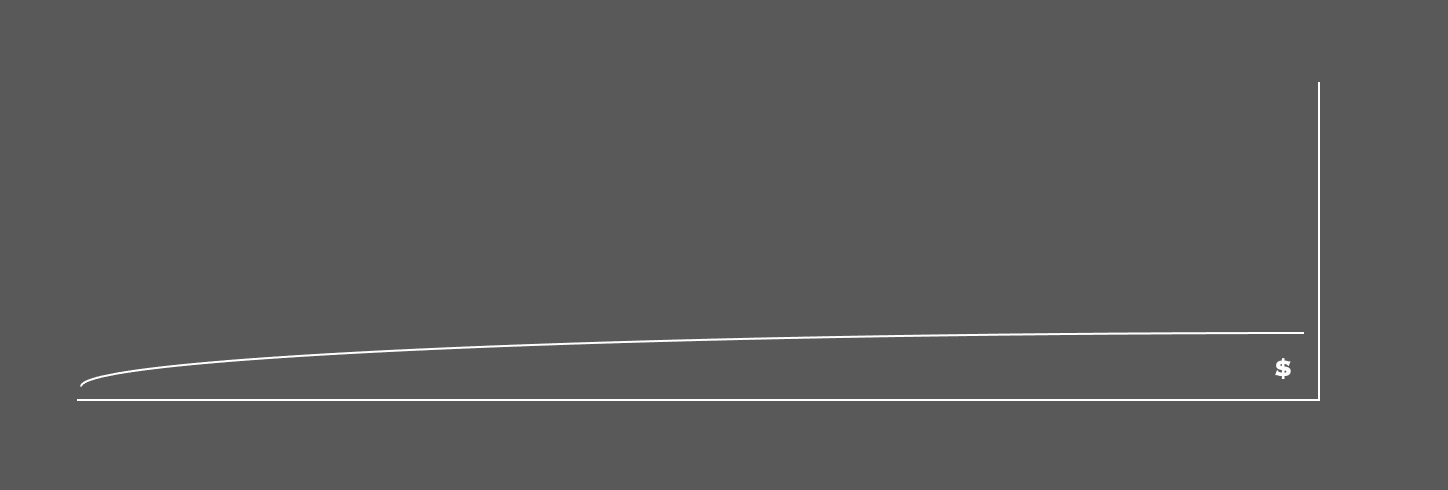
The greater the number of disparate parties and systems that assets need to pass through, the higher the accumulated cost of providing verified authenticity to an end buyer further down the line. While database or blockchain based systems provide solutions for legs of the journey, the integrity of assets (the proof of their uniqueness, completeness and provenance) is still trapped inside that system or platform. Moving that trust from one system to the next is where the reconciliation, settlement, interoperability and integration costs start to pile up as illustrated below.
In many cases with fungible assets like dollars as an example, centralised solutions with interconnected central banks, banks, and payment providers can create workable solutions at scale. Even with these advanced, hyper connected systems quality, cost and time leaves a lot to be desired, especially for those without a seat at the institutional market making table (see our observations on Gamestop and the revenge of main street).
There are multiple levels where digitisation of this scenario can provide improvements, but we hold that a single system or platform of trust to ‘rule them all’ is neither practical nor desirable. These centralised systems create systemic safety and security risks including complex breaches and hacks, with Solarwinds being the latest in a long, continuing line of examples of the increasing fragility that results when we connect a spaghetti of software Jenga towers together. In cases where such systems rule, it is also usually to the detriment of small, medium and even large businesses that are the workhorses of innovation and enterprise and make up at least half of national economies.
The TODA asset and data containerisation can provide an elegant solution that is compatible with any cloud, system, blockchain or device. The container carries the the proof of integrity with it as its ownership is transferred along the value chain and the container and its payload move from one system to the next. The ability for that accumulated proof of integrity to be transferred in seconds with a minimum of energy collapses the reconciliation, settlement and integration costs.
Let’s re-look at our humble pressure gauge destined for the nuclear power plant. Now each digital record and attestation that is linked into the aggregate pressure gauge asset can pass with verifiable integrity between organisational and system silos:
The impact on cost reductions and time can be dramatic, going from exponential cost increases to a flattened logarithmic cost curve, and saving effort on reconciliation and checking, disputes; being able to instantly detect manipulation; and being able to embedded containers with smart rules on handling to reduce administrative and back office burden.
This is a surface treatment of a market issue and solution where we can and will become more detailed in the future, though a few things are worth mentioning at this stage.
First, while the applications and uses of TODA asset containers and the ADOT transaction and room containers are almost unlimited, TODAQ only focuses on providing the ability to create, manage and trade containers. On the back-end we provide distributed infrastructure-as-a-service software for our customers to create and manage their own containers and integrate into their own systems and apps. At the front-end we are delivering a product we call the ADOT Agent that is like a ’Slack’ for Digital Assets, allowing anyone to own any containerized asset and travel anywhere in the ADOT P2P Web to trade with anyone else without brokers. Our customers (cloud & tech services companies, tech dept’s of enterprise and government) have the domain expertise and solutions that are relevant for the P2P markets and supply chains in their specific sectors. As a deeptech company, we just provide the containers. Any errors in the description using the nuclear supply chain above are our own.
Second, this scenario includes physical assets and people, and a very good question is how is the physical world bound together with the containerized digital world in a unified business solution to improve performance, trust or efficiency? This question is probably a whole article series or net new publication like the Digital Credentials Press. We will dive much further into this topic but for now will leave at this. You can containerise credentials for regulators, licensees and vendors and all staff to provide an immutable digital fingerprint proof that is embedded into every containerised file or asset every time a relevant action is taken.
Third, let’s pretend a treated metals supplier right at the start of this supply chain for the pressure gauge parts creates a digital record of the stainless steel they sold to the gauge manufacturer and embedded the proof of their containerized supplier credentials into that asset. That stainless steel file container would become part of the proof of the pressure gauge. The pressure gauge now transfers through multiple parties and is installed in the Nuclear Plant. An inspector shows up much later and inspects the physical gauge and queries the containerized digital asset. The inspector can verify the stainless steel asset container P2P in under a minute but how does the inspector know right away that it really came from the metals supplier and wasn’t some containerized record that was fraudulently added by bad actors somewhere along the route? There are multiple ways to attack this problem in the TODA-ADOT world and doing all of the approaches concurrently would be prudent. For now, we will leave two bread crumbs.
One of the ways we determine authenticity of lineage for people in the physical world is through checking DNA of the parents, and thinking about how the physical world operates is always a good starting point for thinking about how the ADOT Web functions. In the digital container world you can have container ‘file types’ that spawn other containers which contain the cryptographic DNA of the parent. This simple element becomes another powerful check against forgery when employed correctly.
So let’s say the metals supplier created a parent container file type called ‘Supplier X treated metals file type’ and used that to spawn a ‘stainless steel’ asset container they transferred to ownership of the gauge manufacturer and so on down the line. The metals supplier could publish the proof of the file type on their website or ADOT room, but that means the inspector has to go check a third party which seems slow and inconvenient. In the regular http world wide web it is all about websites, and we verify the connection to websites through its SSL certificate which should connect back up through a Trust Chain to a Certificate Authority so we know it is legitimate. In the ADOT Web everything is composed of TODA file containers, and rather than an SSL Certificate Authority we want a file type certificate authority. Which is probably a good place to leave this hanging for now 🧐.
Hassan
If you enjoyed this content and would like to see more, please subscribe to the TODAQ Press here:
Thank you!